Sponsored by Flexera
Sponsored by CA
The Need for Real-Time Risk Analytics
Sponsored by Tata Communicatiions
The State of Organizations' Security Posture as of Q1 2018
Sponsored by Zscaler
Modernizing Malware Security with Cloud Sandboxing in the Public Sector
Sponsored by NICE Actimize
The Sound of Secure Transactions: Voice Biometrics and PSD2 Compliance
Sponsored by Venafi
SSH Study: U.S., U.K. and Germany Executive Summary
Sponsored by Venafi
4 Steps to Protect SSH Keys: Stop Abuse of Privileged Access
Sponsored by BAE Systems
How Dirty Money Moves
Sponsored by IBM
Open Banking in the Digital Era
Sponsored by IBM
Mobile Banking: Contain Fraud and Build User Trust
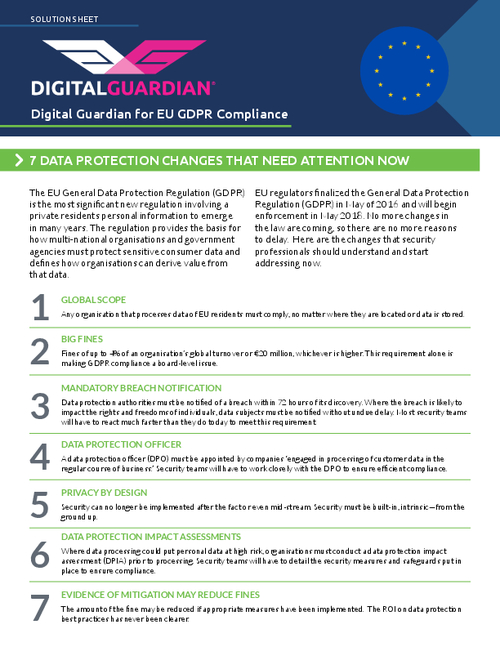
Sponsored by Digital Guardian
A Practical Approach to GDPR Compliance
Sponsored by Digital Guardian
GDPR Compliance Requires Data Loss Prevention
Sponsored by Juniper
Why Organizations Need to Invest More in Testing Their Own Defenses
Sponsored by IBM