Sponsored by Noetic Cyber
Sponsored by RiverSafe
Integrating and Leveraging Threat Intelligence
Sponsored by Riversafe
7 Core Strategies to Optimise your SIEM
Sponsored by JFrog - Microsoft Azure
The Strategic Imperative for Software Supply Chain Security
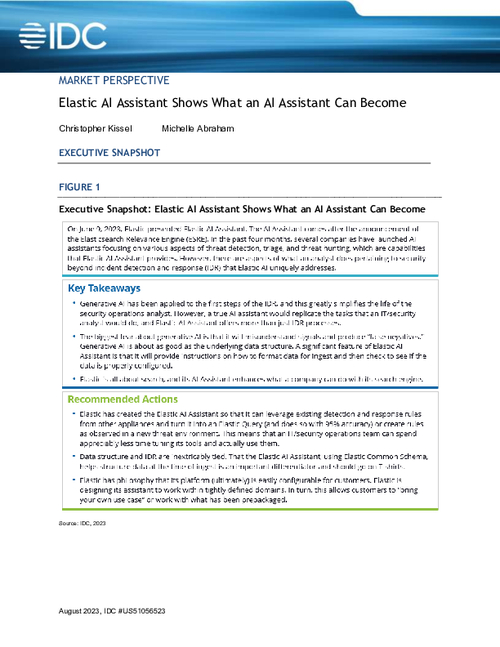
Sponsored by Elastic
Charting the Course: Leading Cybersecurity into a Proactive Era
Sponsored by Verimatrix
Research Survey Report: The State of Enterprise Mobile App Security
Sponsored by Mandiant
The Forrester Wave™️ Threat Intel Service Providers, Q3 2023
Sponsored by RiverSafe
How To Optimise Your SIEM: A Comprehensive Guide
Sponsored by Palo Alto Networks
Software Composition Analysis (SCA) Checklist
Sponsored by Palo Alto Networks
The DevSecGuide to IaC Security
Sponsored by Palo Alto Networks
The DevSecGuide to Kubernetes
Sponsored by Palo Alto Networks
Unit 42 Attack Surface Threat Report
Sponsored by Palo Alto Networks
GigaOm Radar for Attack Surface Management 2023
Sponsored by Palo Alto Networks