Sponsored by ThreatConnect
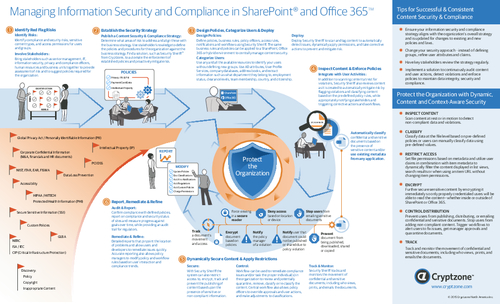
Sponsored by Cryptzone
Managing Information Security And Compliance in SharePoint and Office 365
Sponsored by Cryptzone
The Aftermath Of A Breach and Steps To Reduce Risk
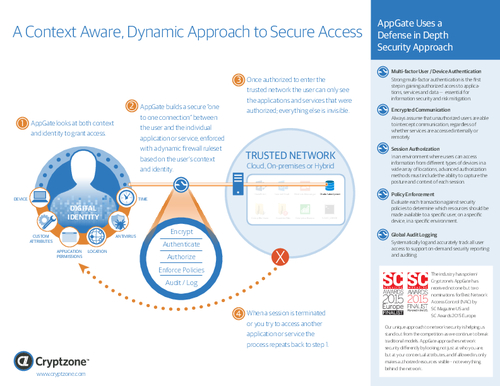
Sponsored by Cryptzone
A Context-Aware, Dynamic Approach To Secure Access
Sponsored by Cryptzone
Four Steps To Readily Achievable Web Accessibility
Sponsored by Cryptzone
After the Perimeter: How A 'Segment of One' Simplifies And Improves Security
Sponsored by HPE Fortify
Internet of Things Security Study: Home Security Systems Report
Sponsored by HPE
The Evolving Era of Big Data
Sponsored by HPE
Breach Response: How to Prepare for the Inevitable
Sponsored by HPE
Orchestrating Enterprise Security in the Cloud
Sponsored by Tenable
2016 Global Cybersecurity Assurance Report Card
Sponsored by Tenable
Cybersecurity is a Business Issue: Enabling Execs to Communicate with the Board
Sponsored by Tenable